
blankcard.stl for 3D printingBecause these files are widely distributed, their signatures are heavily flagged. You can check the detection rate of similar files on VirusTotal .
Generating a technical paper for requires caution, as this file is frequently associated with "cracked" hacking tools, specifically Remote Access Trojans (RATs) or malware builders like Venom Software. Such files often contain hidden backdoors or malware designed to infect the person downloading them.
Do not execute this file on a host machine. If you are using it for educational purposes, ensure you are in a completely isolated, air-gapped virtual machine .
Modifies Windows Registry keys (e.g., HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ) to ensure the malware restarts upon reboot.
Capabilities for building malicious executables (.exe) or DLLs that can be deployed on target machines.
Below is a draft of an analytical report focusing on the security risks and technical characteristics typical of this software version.
Technical Analysis: Venom Cracked 2.7.0.0 (Malware Analysis Report) 1. Overview
Reach us via email if you can help.
Many thanks to our supporters and contributors who have joined us in this pursuit of preserving this segment of digital history:
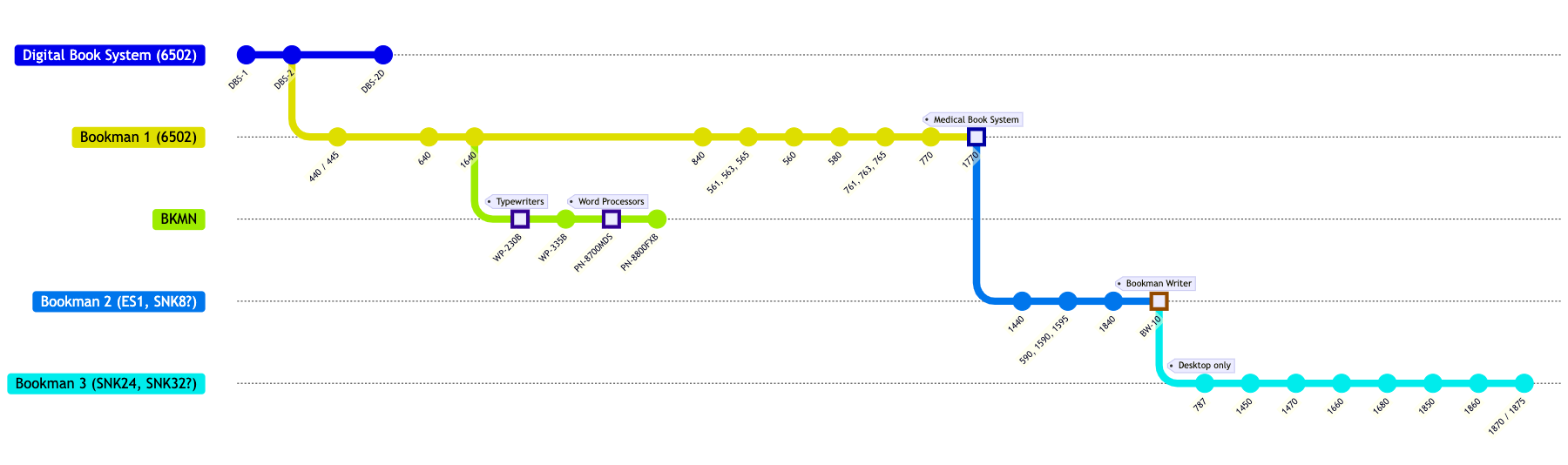
Bookman system compatibility chart coming soon.
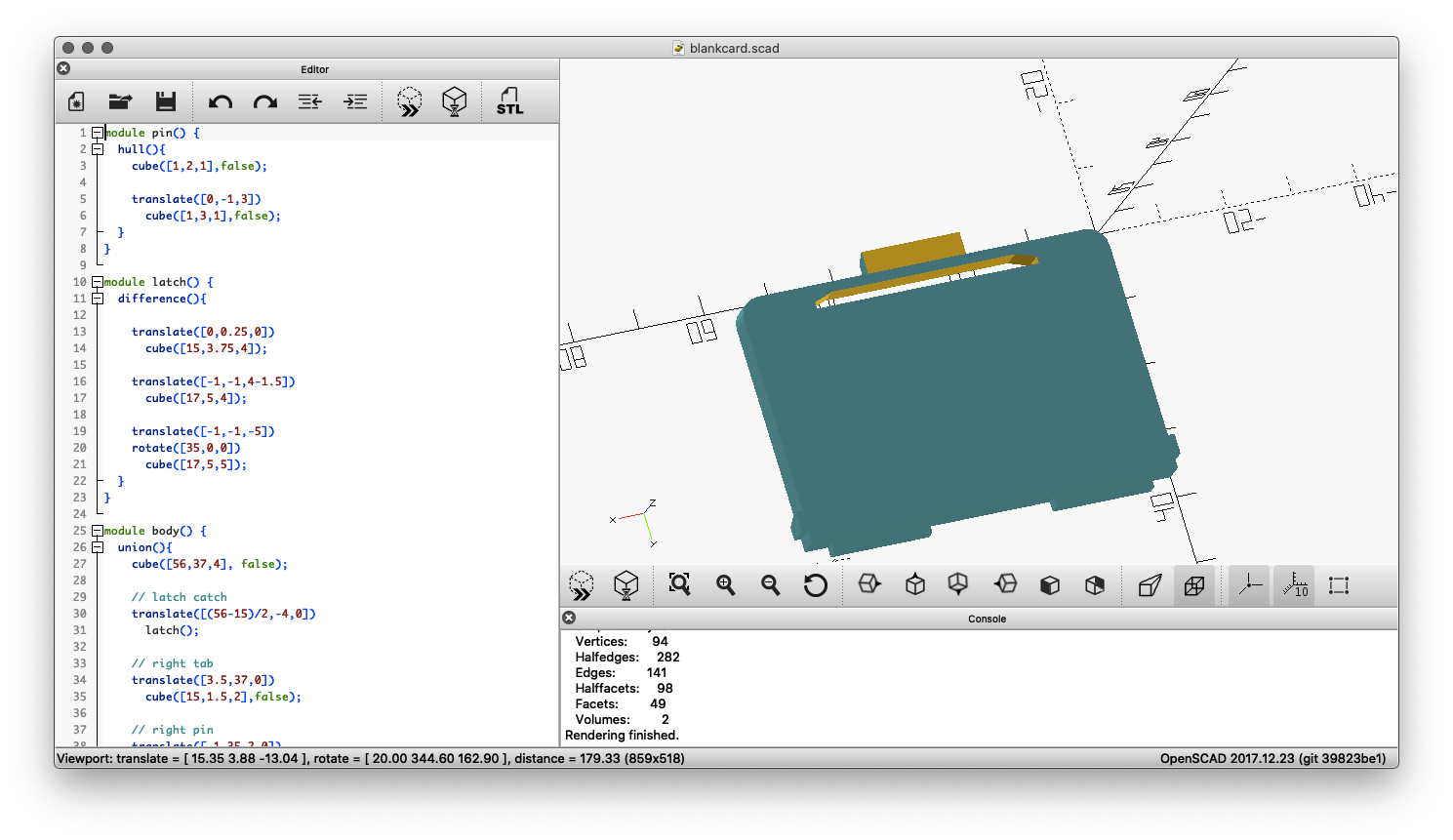
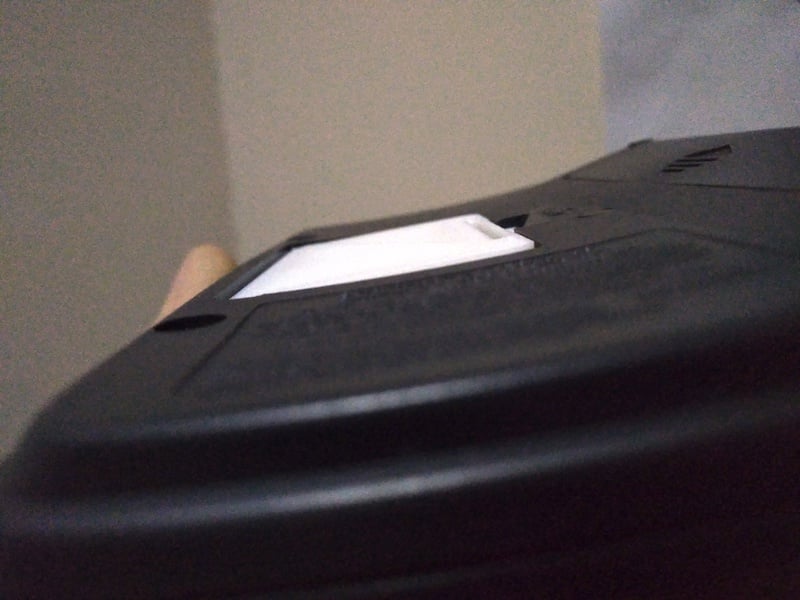
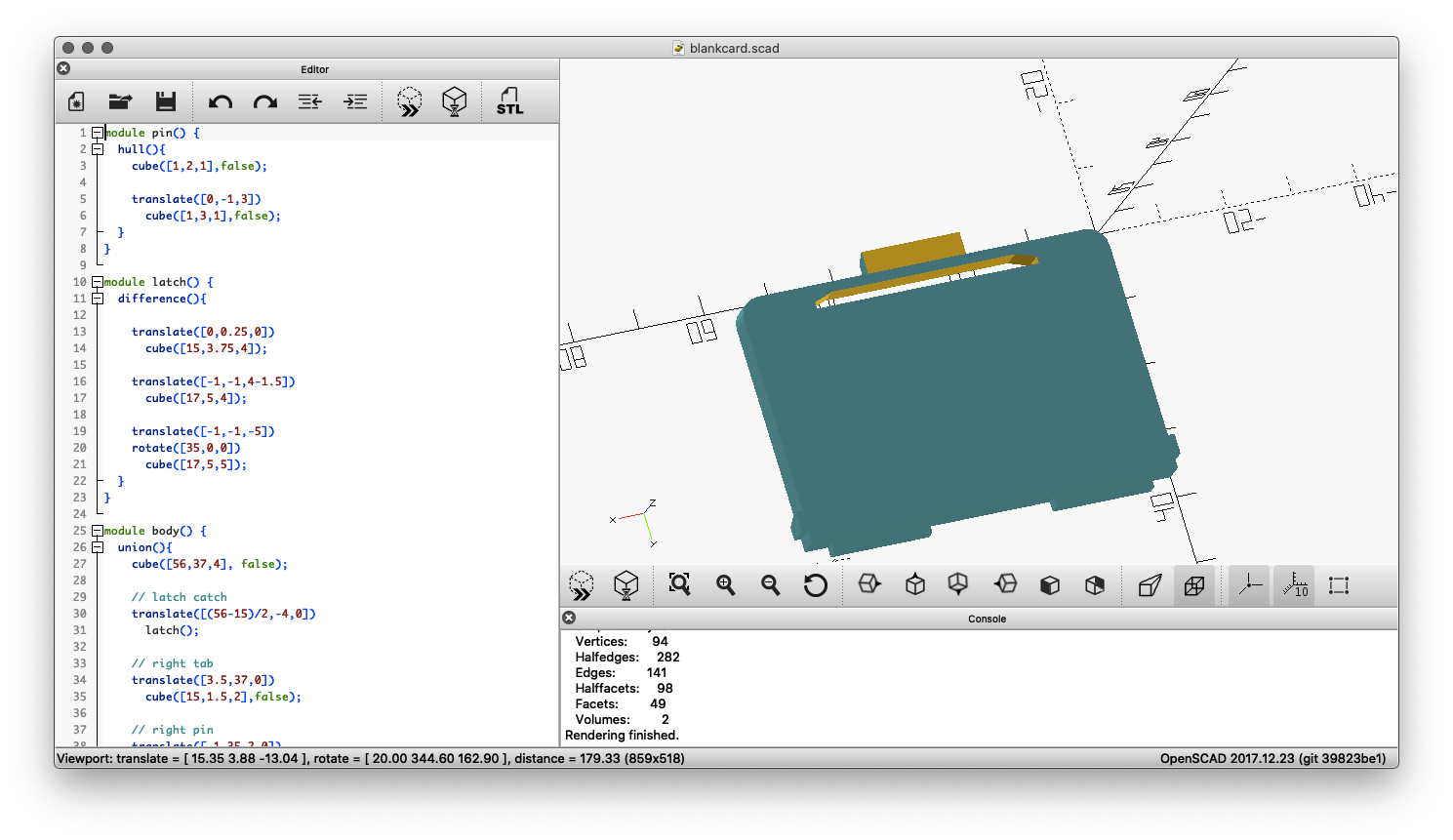
This 3D printable card blank will ensure your Bookman cartridge contact strip stays clean and sits flush with the rest of the device by filling the card slot.
 |
 |
 |
Download blankcard.stl for 3D printing |
||
This tool is used to create replacement labels for Franklin BOOKMAN cartridges that have faded or otherwise deteriorated labelling. The generated labels are downloadable as SVG files and can be printed at 100% scale for a 1:1 reproduction size suitable for application on worn ROM cards.

See the source code for this tool here.
You can find scans of various Franklin promotional / catalog leaflets below. Items listed in chronological order.
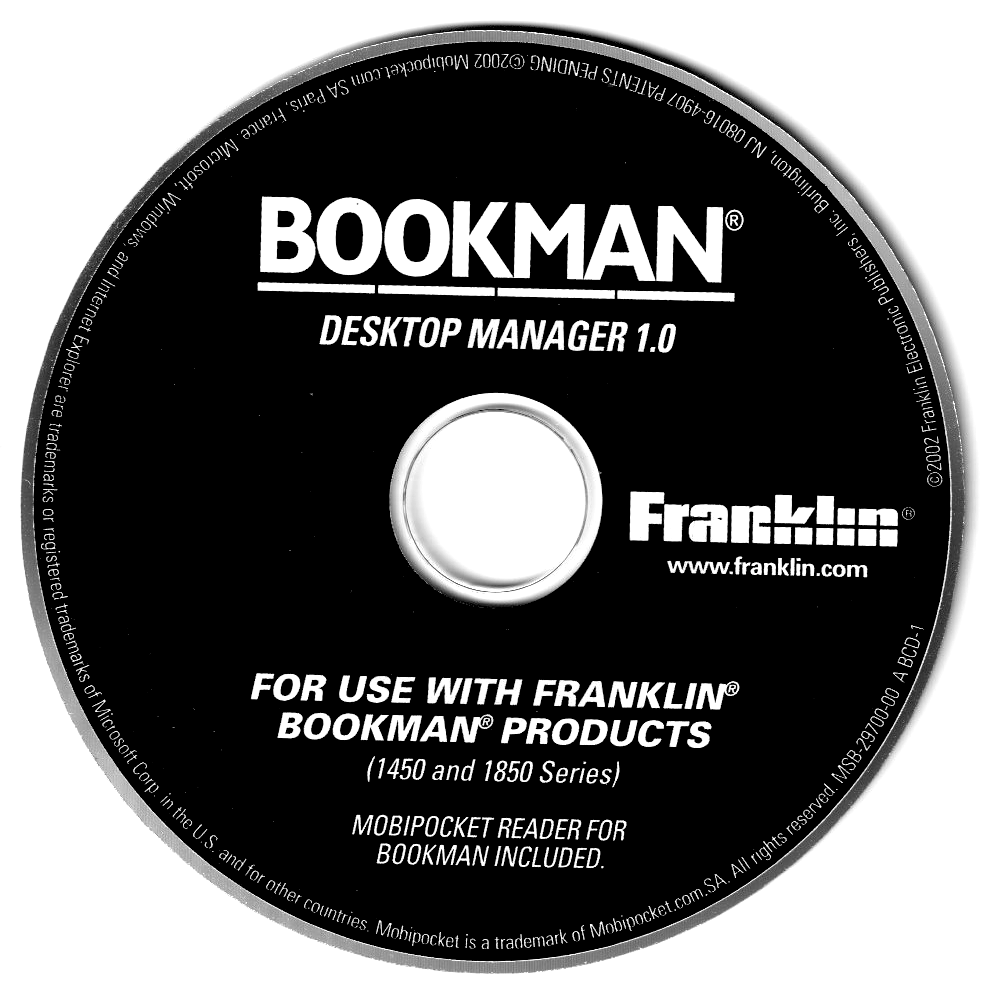
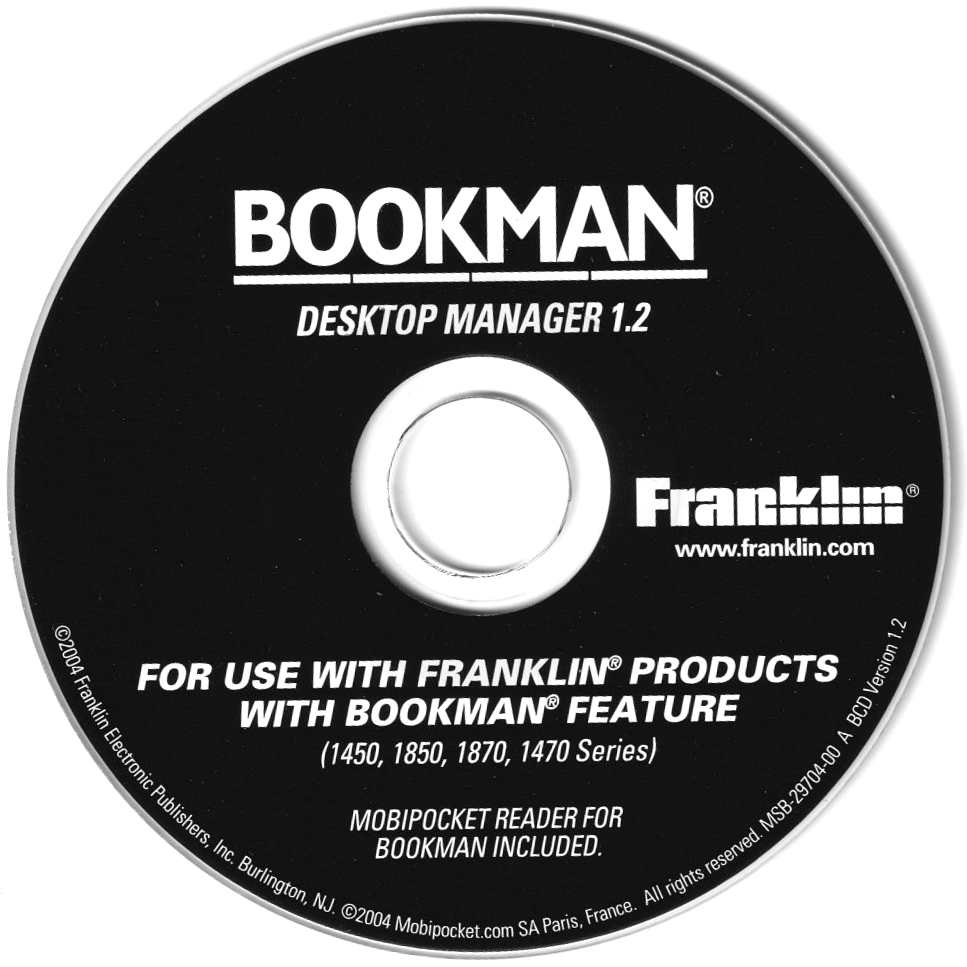
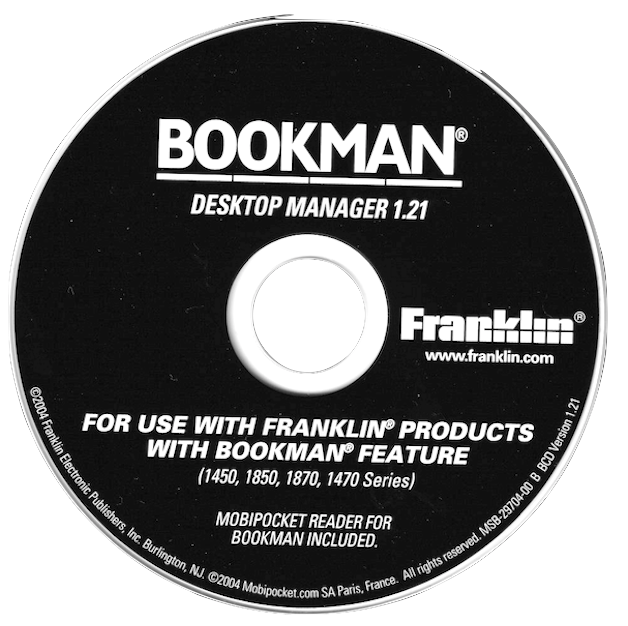
This is a collection of disk images and files of related software that came bundled as part of various Franklin DBS / Bookman devices. Click to download these files.
|
|
|
|

|
|
|
FEP received its own official number in the USB vendor code list after submitting it to the USB consortium: 0x09b2 (hex) or 2482 (dec). The submission was related to use of USB for the eBookman device.
CK2FRK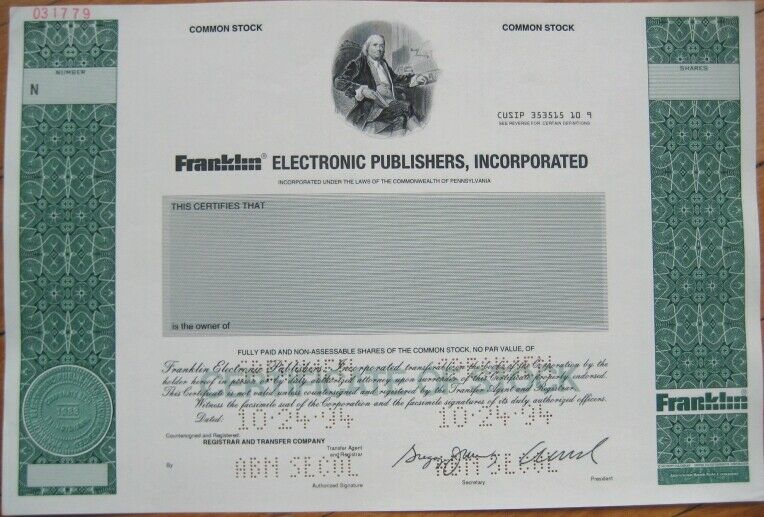
Because these files are widely distributed, their signatures are heavily flagged. You can check the detection rate of similar files on VirusTotal .
Generating a technical paper for requires caution, as this file is frequently associated with "cracked" hacking tools, specifically Remote Access Trojans (RATs) or malware builders like Venom Software. Such files often contain hidden backdoors or malware designed to infect the person downloading them. Venom Cracked 2.7.0.0.rar
Do not execute this file on a host machine. If you are using it for educational purposes, ensure you are in a completely isolated, air-gapped virtual machine . Because these files are widely distributed, their signatures
Modifies Windows Registry keys (e.g., HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ) to ensure the malware restarts upon reboot. Such files often contain hidden backdoors or malware
Capabilities for building malicious executables (.exe) or DLLs that can be deployed on target machines.
Below is a draft of an analytical report focusing on the security risks and technical characteristics typical of this software version.
Technical Analysis: Venom Cracked 2.7.0.0 (Malware Analysis Report) 1. Overview
Did you find this topic interesting? Check out other projects like this one!